This guide provides comprehensive system requirements and environment preparation steps for installing Package Security Manager. Before beginning installation, make sure your system meets all listed requirements and complete the necessary environment preparation steps for your system setup. Anaconda recommends installing Package Security Manager in a dedicated environment.Documentation Index
Fetch the complete documentation index at: https://anaconda.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Hardware requirements
CPU/Processor specifications
- Minimum 4 CPU/Processor cores
- Must support x86-64-v2 architecture
- Must support SSE4.2 instruction set
Memory
- Minimum 16GB RAM
Storage
- Minimum 1.5TB available storage (standard installation)
- Minimum 2.0TB available storage (air-gapped installations)
When partitioning space, allocate 20GB for
/var/lib and the remaining 1.5TB for /opt/anaconda.Our recommended storage space only accounts for Anaconda’s default ; if you want to additional channels or upload additional , please allocate additional storage accordingly.
Software requirements
Operating system
- RHEL/CentOS 7.9 or later
- Ubuntu 20.04 or later
- Other Linux variants with full Docker/Podman support (contact Anaconda implementation team for current approved distributions)
Container runtime requirements
- Docker requirements
- Podman requirements
- Docker Engine 23.x+ (Supports Compose format 3.8)
- Docker Compose 2.1+ (Supports Compose format 3.8)
- The default log driver must be configured to the json-file.
For Red Hat systems, please refer to the Default options for modifying docker daemon options.To verify the default log driver is configured to the json-file, run the following command:
External database requirements
Package Security Manager supports Postgres versions 9.6 through 14.9 for external database server use. If you are using an external Postgres server, complete these steps to create thekeycloak and anaconda users and assign them a role with appropriate permissions prior to installation.
External Postgres setup instructions
External Postgres setup instructions
- Log in to your Postgres server.
-
Create the
keycloakandanacondausers, and set passwords for them by running the following commands: -
Create the databases needed for your users by running the following commands:
-
Create the role needed to configure permissions for the
keycloakandanacondausers, then assign them the role by running the following commands:
Security considerations
The following security software must be temporarily disabled during installation:- SELinux
- CrowdStrike
- FIPS
- Other system hardening software
Security software can be re-enabled after installation is complete.
SSL requirements
Package Security Manager can use TLS/SSL certificates to provide transport layer security for the cluster. If you do not have these certs prior to installation, self-signed certificates can be generated during the initial installation. You can configure the platform to use organizational TLS/SSL certificates after completing the installation. You can purchase certificates commercially, use Let’s Encrypt, or generate them using your organization’s internal public key infrastructure (PKI) system. When using an internal PKI-signed setup, the CA certificate is stored on the file system. You will need to make sure that the root certificate of your certificate authority is trusted by the server running the application and the workstations used by users of the application. In all cases, SSL configuration requires the following:- A certificate for the root certificate authority (CA)
- An intermediate certificate chain
- A server certificate
- A private server key
DNS requirements
Web browsers use domain names and web origins to ensure security isolation between sites. If you plan to use DNS, you must have it ready prior to installation. This DNS name is what users will use to access the application.Port requirements
External ports
It is important to protect all services running on the node from outside access. The following ports need to be open to allow access to Package Security Manager via browser and (optionally) via SSH::443nginx - only if you are using HTTPS:22ssh - optional; only if you need SSH
Internal ports
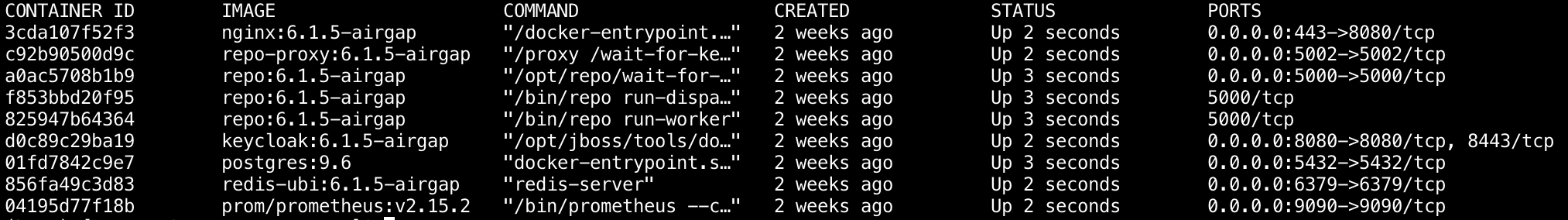
Package Security Manager uses several ports for internal communication between components. These ports are open on Docker containers and exposed only to the Docker network. These ports do not need to be open to the end user, but they do need to be reserved, as some bind to the local host network interfaces::5000repo - Package Security Manager API:5002repo-proxy - Package Security Manager file serving API proxy:5000repo-dispatcher - Package Security Manager event dispatcher/handler (exposed only for Prometheus metrics):5000repo-worker - Package Security Manager scheduled jobs worker (exposed only for Prometheus metrics):8080keycloak - Keycloak’s/auth/*endpoints are proxied in Nginx:5432postgres - PostgreSQL database used by Package Security Manager and Keycloak:6379redis - Redis instance used by Package Security Manager services:9090prometheus - Prometheus is proxied in Nginx at/prometheus
To change user passwords after installation:
- For
postgres, run\password postgreswhen in the shell of the Postgres container. - For
redis, follow the instructions under Troubleshooting.
Network requirements
URL allowlist configuration
Allowlist the following URLs in your firewall:https://repo.anaconda.com/https://repo.anaconda.cloud/https://anaconda.org/https://anaconda.com/https://api.anaconda.cloud/https://conda.anaconda.org/https://pypi.org/https://files.pythonhosted.org/https://cran.r-project.org/(optional - for CRAN R users)
Network communication configuration
To allow containers to communicate with one another on your host, enable IP address forwarding using these commands:System validation checks
Once you have prepared your environment to meet the requirements, validate your system configuration by running the following commands: Check processor and CPU details:docker-compose version:
Additional preparation steps for air-gapped environments
Air-gapped installations of Package Security Manager require additional setup steps to obtain the package files that will populate your , then place them in the correct location.Downloading packages and CVEs
In this section, you will download Package Security Manager packages and .Downloading Package Security Manager Packages may take several hours.
All platforms
All platforms
Run the following commands to download the Anaconda repository for all platforms:Run the following commands to download the corresponding checksum files:
Downloading the
conda_msys2.zip and conda_r.zip files is optional.Windows airgap files
Windows airgap files
- Main for Windows
- R for Windows
Run the following commands to download the Run the following commands to download the corresponding checksum files:
main repository for Windows systems only:Linux airgap files
Linux airgap files
- Main for Linux
- R for Linux
Run the following commands to download the Run the following commands to download the corresponding checksum files:
main repository for Linux systems only:macOS airgap files
macOS airgap files
- Main for macOS
- R for macOS
Run the following commands to download the Run the following commands to download the corresponding checksum files:
main repository for macOS systems only:Validating Packages and CVEs
To ensure that the files you’ve downloaded have not been tampered with, you must verify the integrity of the.zip files by running commands to generate their SHA-256 cryptographic hashes (or “checksums”) and the cryptographic hashes for their corresponding .sha256 files, then checking the output to be sure they match. Choose a set of commands that corresponds with your setup:
File verification commands
File verification commands
- On Windows
- On Linux /macOS
If you downloaded your repository files on a Windows machine, run the following commands to view the hashes for the files:
You must run these commands for each file you downloaded.